Epic Fury & Lion’s Roar How Military Ops Mirror Cyber Deception
Operations “Epic Fury” (U.S.) and “Lion’s Roar” (Israel) are not just feats of firepower and precision. They are masterclasses in strategic deception. In both cases, the decision makers did not just plan strikes. They planned misperceptions, false signals, and carefully staged appearances so that Iran’s early warning systems and intelligence machinery would see the “wrong” picture until it was too late. Those same deception principles, masking true intent, manipulating expectations, and luring adversaries into predictable patterns, sit at the heart of modern cyber deception, including Deceptive Bytes’ endpoint centric Active Deception platform.
How Israel deceived Iran before “Lion’s Roar”
Long before the first missile lit up the skies over Iran, the IDF (Israel Defense Forces) and its allies ran a campaign of strategic and operational deception. Senior officials deliberately maintained a routine public and satellite visible image of normalcy, even as forces prepared for a massive strike. One vivid example is that on the eve of the operation, the IDF Chief of Staff and his aides returned late from what looked like an ordinary family dinner, deliberately using private or non official cars so that the official vehicles did not cluster at the Kirya headquarters. This meant that from satellite imagery Iran could see, the Ministry of Defense appeared as an empty, routine night compound, not a hub of final hour war planning.
Beyond personal level tricks, Israel and the U.S. ran a broader narrative deception. Leaks about “upcoming family events,” “routine diplomatic talks,” and “vacation plans” were designed to lower Iran’s pulse of alert. By feeding Tehran a story of political calm and domestic preoccupations, Israel helped delay the perception of an imminent attack, compressing the time Iran had to disperse forces or harden command centers. At the same time, behind that curtain, hypersonic and precision guided munitions were being positioned, electronic warfare suites tuned, and air wings readied, all while the adversary’s sensors were still tuned to the “normal” baseline.
Tactical deception during “Epic Fury” and “Lion’s Roar”
The deception did not end with pre-strike misdirection. “Epic Fury” and “Lion’s Roar” leaned heavily on temporal deception and expectation bias. Iran’s planners expected a nighttime attack, but the U.S. and Israel struck in broad daylight. That mismatch between expectation and reality degraded Iran’s reaction cycle, because its procedures, alert shifts, and command routines were optimized for a night time scenario. Radar and command centers that were “on holiday” mentally suddenly had to manage a major inbound raid, without the cover of darkness.
Another layer was the use of advanced reconnaissance and sensor manipulation. Reporting on earlier Israel-led operations suggests that Iranian radar and surveillance systems were flooded with decoy drones, spoofed signatures, or ambiguous traffic so that operators could not distinguish between “routine” and “threatening” patterns. That same concept, confusing the enemy’s sensors with false or noisy signals, is exactly what cyber deception tools do when they scatter fake credentials, honey paths, and phantom endpoints across a network.
The deployment of U.S. F 22 Raptors to Israel in the days leading up to the operations also served a dual purpose: overt deterrence and covert camouflage. Publicly, the arrival of these advanced stealth fighters signaled U.S. readiness and commitment, which could provoke Iran into a predictable posture. Privately, it also created a new “normal” baseline for Iranian SIGINT and satellite watchers. More jets, more noise, more activity. Once that baseline was established, the actual strike packages could be disguised inside the expanded air traffic pattern, making it harder for Iran to distinguish rehearsal from real time execution.
From battlefield deception to cyber deception
On the battlefield, deception is about violation of expectation. Making the enemy see a calm sky while the fleet is outbound, or a quiet headquarters while the command team is secretly in motion. In cybersecurity, the same playbook applies, only the battlefield is the memory and file system of an endpoint.
Traditional defenses such as EDR and gateways wait for an attacker to manifest malicious behavior, unusual process behavior, encrypted exfiltration, or registry changes, after the attacker is already inside. Cyber deception, by contrast, assumes the attacker will probe, enumerate, and move laterally. It simply ensures that the first things they see are bait rather than real assets. Deceptive Bytes’ Active Deception, for example, weaves deceptive artifacts, fake credentials, decoy services, and illusory lateral paths, into the live memory of every endpoint. A legitimate user does not encounter these traps. Only an intruder who is actively exploring the system will.
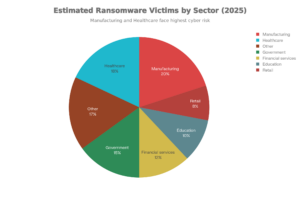
Why today’s “Epic Fury” style threats need endpoint deception
Endpoint deception with Deceptive Bytes is like turning each endpoint into a fortress that appears heavily guarded so that malware’s evasion and reconnaissance techniques immediately reveal themselves. Instead of hiding the real assets, the environment is designed to look so secure and instrumented that any suspicious behavior such as credential hunting, lateral movement probing, or memory scanning trips built in traps and triggers early detection or termination before the malware can settle in.
In the context of “Epic Fury” and “Lion’s Roar,” the IDF and U.S. forces did not just react to missiles in the sky. They sought to degrade the adversary’s ability to launch in the first place. Cyber deception aims for the same goal. Instead of waiting for a ransomware payload to detonate, it seeks to stop the attacker in the reconnaissance and lateral movement phase, when the cost of interception is lowest and the impact on the business is still near zero.
Operational deception in practice: Deceptive Bytes as “Kirya camouflage” for the endpoint
If you think of your enterprise network as the Kirya headquarters, every endpoint is a potential window into that HQ. Cyber deception tools like Deceptive Bytes are the “non official cars” of cybersecurity. They make the environment look normal to the casual observer while hiding the real command structure and high value assets.
By scattering realistic looking decoys across users, servers, and cloud workloads, Deceptive Bytes creates a scenario where any attacker that persists beyond the perimeter will eventually, and intentionally, touch a trap. That trap signal is not a guess. It is a high fidelity indication of an active adversary, which shifts the security posture from reactive logging to proactive engagement and containment.
In short, “Epic Fury” and “Lion’s Roar” show that modern warfare is as much about misperception as it is about missiles. In cybersecurity, the equivalent is Active Deception. Turning the attacker’s assumptions, routines, and search patterns against them, so that the first move they make inside your network is also the first move you see.
Don’t Miss a Thing
Sign up today and we’ll send an email when new posts come out.
We collect and use this information in accordance with our privacy policy.